Stolen NFTs Part 2: A Nexus of Big Accounts

Over the last 18 months, we estimate 886 NFTs across seven prominent collections have been marked as suspicious or stolen by OpenSea, the world’s largest NFT Marketplace.
The total value of transactions involving these assets since then exceeds $140 million, according to Hoptrail data and information available on Dune Analytics.
Dune Analytics data estimates that more than 1,000 NFTs in total have been marked as stolen or suspicious across these collections. But that doesn’t tell the full story.
We dig into the data to assess the nexus of accounts apparently central in trading stolen or suspicious items. Lets first look at the collection details:
Bored Ape Yacht Club: 820 transactions (ETH 45,083)
Mutant Ape Yacht Club: 706 (ETH 16,611)
Bored Ape Kennel Club: 637 (ETH 3,989)
Azuki: 525 (ETH 8,666)
Clonex: 441 (ETH 6,691)
Doodles: 250 (ETH 3,088)
Moonbirds: 212 (ETH 4,197)
OpenSea has been marking NFTs as suspicious or stolen since mid-2022. These flags are based on reports filed by previous owners. Buying and selling of those assets is then halted on the platform.
There is no timestamp showing when an asset was marked as suspicious; we cannot be certain that all transactions occurred when an embargo was placed on the asset. It also means that not all sellers of stolen NFTs should be viewed as suspicious, particularly when a red flag was assigned retrospectively.
More importantly, sales of marked assets continue to occur on other platforms, most notably LooksRare. LooksRare, the world’s second largest NFT marketplace, does not have a red flag mechanism like OpenSea or its rival X2Y2, which does flag and embargo assets when listed by OpenSea.
We touched briefly upon the issue of communication between marketplaces in Part 1, which you can find here.
Big Whales
What we can discern from the data is insight on buyers and sellers. This includes accounts that appear frequently as sellers of stolen goods.
For this analysis, we have removed accounts which are tied to exchanges and other marketplaces. In some isolated cases we see prominent collectors or creators in the list. For instance, Pranksy, a well-known NFT investor, appears 18 times as a seller of suspicious/stolen goods, most likely due to the volume and breadth of their activity.
This leaves us with nine accounts that have each sold more than 10 suspicious/stolen items in the past 18 months. Sales by these accounts totals 142, generating revenues of ETH 3,239 (5.3 million).
Top sellers of NFTs listed as stolen/suspicious by OpenSea
0x2d1
The top account in the list goes by the moniker ‘CheaperOnX2Y2’ on OpenSea. Or at least it used to. It’s OpenSea account has now been deleted or removed, last trading a marked NFT almost six months ago.
Revenue from CheaperOnX2Y2 sales far outstrips other sellers. There are several interesting characteristics with its sales, however, that suggest it is directly linked to the suspicious activity.
Its biggest seller, BAYC #8166, was offloaded (flipped for a sizeable profit) in April 2022, around the time when the asset was flagged by OpenSea.
Its second highest grossing asset, BAYC #5373, was sold following a succession of quick transfers and back-to-back sales on OpenSea and LooksRare - often indicators of suspicious activity.
A third, BAYC #5171, followed a similar pattern. A sudden transfer from the original owner to a new address is the first indicator of unusual activity. Then followed a series of additional transfers and sales on OpenSea and LooksRare.
Notably, CheaperOnX2Y2 was transferred this asset from another wallet, before selling on LooksRare for ETH 90. Blockchain data confirms a number of prior transactions between CheaperOnX2Y2 and this intermediary, pointing to potentially deeper ties between the addresses.
While it is possible that CheaperOnX2Y2 unwittingly handled stolen NFTs, the patterns raise alarms. We also know it has links to other - more concerning - addresses in the list.
Arthur0x Hacker
The second address in the list is more popularly known as the Arthur0x Hacker. In March 2022, the wallet of crypto personality Arthur0x was hacked, resulting in the theft of Clonex and Azuki NFTs. These assets were immediately sold, resulting in a windfall of ETH 200 for the hacker.
Indirect recipients of these assets include CheaperOnX2Y2. Hoptrail data confirms it traded heavily with an Arthur0x Hacker intermediary address around the time of the hack. That intermediary purchased 9 of the 15 NFTs from the Arthur0x Hacker, suggesting that it is connected to al least one of the two parties.
Lets take Azuki #6637 as an example. That asset was stolen by the Arthur0x Hacker on 22 March 2022. It was then sold to the intermediary - at below floor prices - and then transferred immediately to CheaperOnX2Y2, which sold the asset for a profit. All on the same day.
The exact same pattern is seen with Azuki #4365. At exactly the same prices. On the same day.
The same goes for #8659, #7322, #4759, and #7569, as well as Clonex 9233. The same addresses, the same pattern, the same prices. The same outcome.
Arthur0x Hacker’s wallet on Hoptrail, containing a large number of Second Self NFTs
Moonbirds Hacker
On 26 May 2022, Digitalornithologist.eth was hacked, resulting in the loss of 29 Moonbirds valued at about ETH 750. The culprit was 0x7cc, better known as ‘volvo_cars_lover’ (a now-deleted OpenSea profile) or peugeot_car_123, their current LooksRare moniker.
Major destinations of funds from volvo_cars_lover are Tornado Cash or Tornado Cash depositors. Funds to the mixer total over ETH 300, more than covering the ETH 252 revenues from the stolen assets. These addresses are likely controlled by the same person.
There is a lot going on with this address, as you can see from Hoptrail’s Explorer.
Red flag tags on the Moonbirds Hacker
Unusually, around half of the assets appear to have been transferred back to Digitalornithologist.eth in June. The rest were sold, with two addresses picking up two each:
0xfb9 (alias Common Ground Liquidity), which is third in our list. It also comes fourth in our top buyers list of stolen assets, with 17.
0xb4d (g3f), which has sold six suspicious/stolen assets and has bought 11.
0xfb9 has, on at least three occasions, received or sold MAYCs below the floor price. The pattern could simply be that of an unwitting opportunist - picking up stolen assets at lower prices as part of a fire sale.
In one instance, in April 2022 the account received MAYC #2240 from 0x79c (fifth in our list). 0x79c was connected to an infamous BAYC Instagram scam in the same month. 0xfb9’s OpenSea account, unlike others, remains active.
BAYC Instagram Hack Connections
Lastly, we come to 0xa9e and 0x79c – fourth and fifth in the list. Both are connected (via deposits) to a BAYC Instagram hack in April 2022. The first address, better known as ‘Z4S’ has deposited more than ETH 130 to the hacker’s address, making it its top source of funds (except for LooksRare). For its part, 0x79c has purchased at least one stolen MAYC (#16500).
So, links are evident among prolific sellers in the NFT space. Many have ties (direct or indirect) to phishing scams and hacks, whilst others appear to serve as intermediaries or unwitting buyers of stolen goods.
And while we can identify some egregious behaviour, the issue is clouded by a lack of red flag data from marketplaces, including timestamps on flagged assets as well as better cross-platform communication on NFTs that are marked as suspicious.
For now, several outlets remain for hackers even if assets have been frozen on OpenSea.
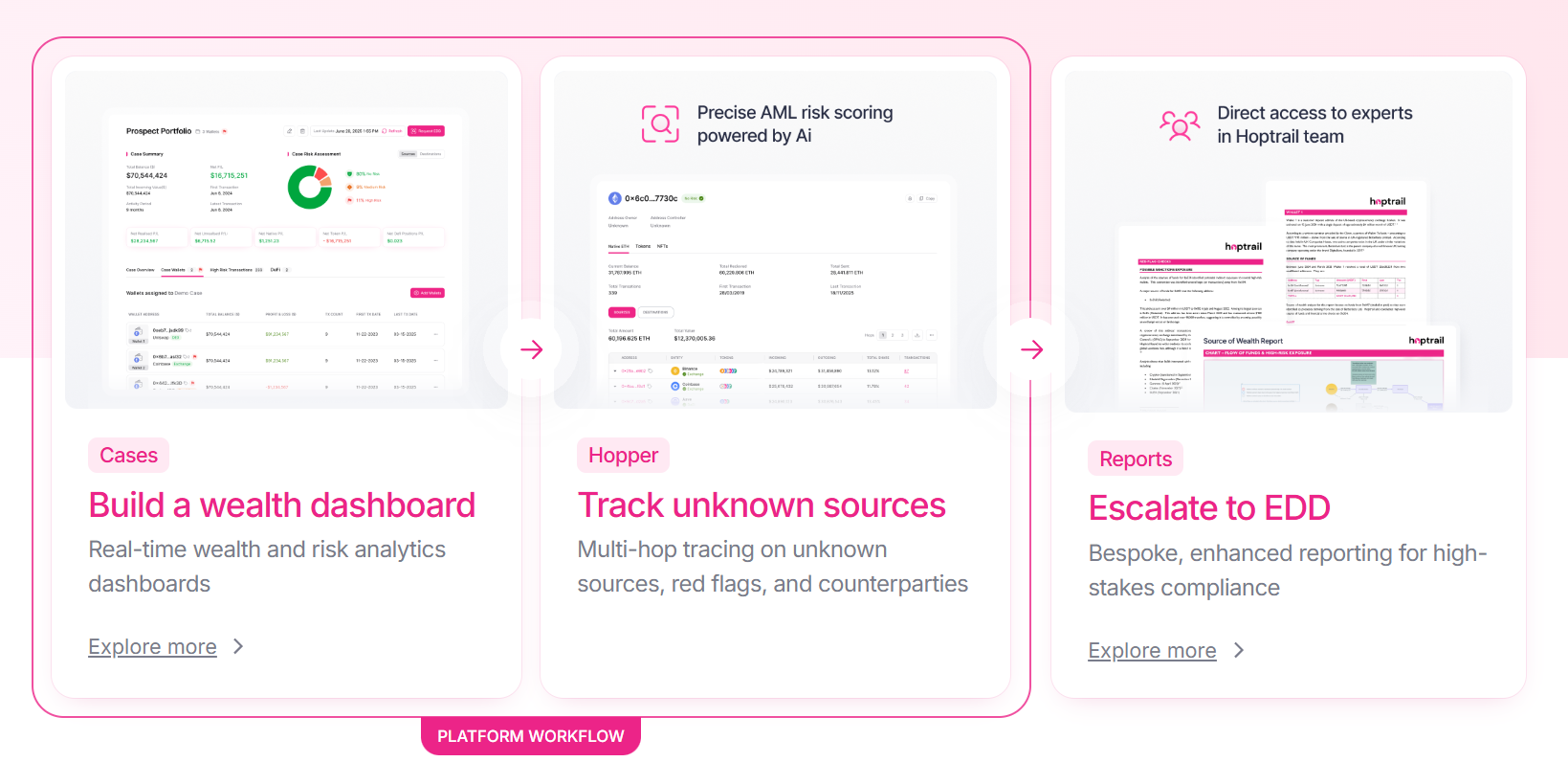
Onboarding Crypto HNWIs: The Complete Guide

Hoptrail partners with Weatherbys Bank
Hoptrail 2.0
Subscribe to the Hoptrail newsletter
Sign up with your email address to get the latest insights from our crypto experts.
